CMMC
Find an MSP
It is here the DoD has finally ruled on CMMC – what does this mean? What level should you be?
What systems are in scope – which ones are out of scope? How do I prepare?
Do all my endpoints require compliance? What if I use VDI or AVD?
- IT IS HERE – THE DOD HAS FINALLY RULED ON CMMC – WHAT DOES THIS MEAN?
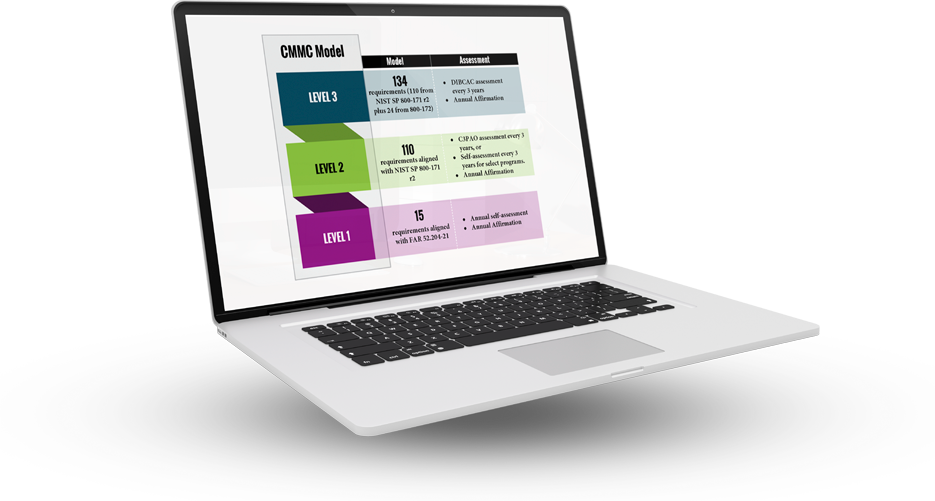
- WHAT LEVEL SHOULD YOU BE?
- WHAT SYSTEMS ARE IN SCOPE – WHICH ONES ARE OUT OF SCOPE?
- HOW DO I PREPARE?
- DO ALL MY ENDPOINTS REQUIRE COMPLIANCE?
- WHAT IF I USE VDI OR AVD?
- CMMC (Cybercecurity Maturity Model Cerification)
ALL OF THESE QUESTIONS ARE NOT EASY TO ANSWER - THEY
ARE COMPLICATED, BUT AT CLOUD2E LLC - WE CAN GUIDE YOU
THROUGH THE ENTIRE PROCESS AND SUPPORT THE ENCLAVE FOR YOU ON AN ON-GOING BASIS.
SECURING SENSITIVE DATA: A Trusted Partner for Cybersecurity Solutions
We have over 20 years of technical expertise with implementing secure and compliant cybersecurity solutions for federal government entities, the intelligence community, defense contractors, and commercial companies in Reston, VA. We align our clients’ operations with Cybersecurity Maturity Model Certification (CMMC) standards and other federal requirements.
Our expertise extends to assisting organizations in adopting secure cloud solutions while maintaining compliance with stringent cybersecurity frameworks.
THE IMPORTANCE OF CMMC COMPLIANCE
CMMC compliance is a set of cybersecurity standards established by the United States Department of Defense (DoD) to safeguard sensitive information across various sectors. It provides a structured framework for implementing robust cybersecurity. measures, reducing the risk of data breaches and unauthorized access to sensitive information.
In addition to enhancing the overall security posture of Reston, VA, organizations, adherence to CMMC standards enhances the organization’s credibility and trustworthiness, particularly when engaging in contracts with federal government entities.
REGULAR SECURITY ASSESSMENTS
Regular security assessments are an essential part of any cybersecurity framework, with the aim of proactively identifying potential vulnerabilities in an organization’s network, software, or hardware.
Cyber attackers are constantly evolving their tactics, and regular security assessments can proactively address any potential security gaps and enable organizations to adapt and strengthen their defenses accordingly. We offer regular security assessments in Reston, VA, to address security gaps before they can be exploited by cyber attackers.
VULNERABILITY SCANNING
Vulnerability scanning plays a critical role in identifying security risks within IT infrastructure. We use specialized tools and techniques to scan your systems for any susceptibility that could be exploited by malicious actors. This proactive approach allows the patching of any weaknesses before they can be exploited by cybercriminals. We offer vulnerability scanning services in Reston, VA, to enhance the overall security posture of businesses and organizations, and to establish a robust defense against cyber threats.
DATA PROTECTION
Ensuring the security of customer information, financial records and intellectual property is vital for maintaining trust with stakeholders and complying with data protection regulations. We offer custom solutions to Reston area businesses that are designed to safeguard sensitive data at every level from unauthorized access, breaches, and theft.
From advanced encryption technologies to secure data storage and network security protocols, we have extensive experience in providing Reston, VA, businesses and entities with cutting-edge data protection solutions. Our solutions are tailored to ensure that organizations can meet and exceed regulatory requirements, thus avoiding potential penalties and legal implications associated with non-compliance.
INCIDENT RESPONSE PLANNING
In the event of a security breach or cyberattack, having a well-defined incident response plan in place is essential. We can develop a comprehensive incident response plan for Reston area companies and entities to define the specific actions that will need to be taken in the event of a security breach or cyberattack. An incident response plan will enable swift and effective actions to minimize the impact on your organization. This can help reduce potential financial losses, legal liability and reputational damage.
PREVENTION OF CYBER THREATS
Cyber threats can take on various forms, posing serious risks to the digital assets of Reston area businesses. These threats can include malware, phishing and ransomware attacks. The potential for cyberattacks is a constant concern for organizations of all sizes.
We offer tailored cybersecurity solutions to address these potential security challenges. This can include educating employees on best practices for identifying and responding to potential threats, leveraging advanced antivirus and firewall solutions, and conducting regular security assessments.
MAINTAINING BUSINESS CONTINUITY
The ability to promptly resolve security issues in the event of a security incident is crucial. A strong cybersecurity posture can help maintain business continuity by quickly identifying and resolving security issues, minimizing downtime, and ensuring uninterrupted operations.
In conclusion, Cloud2E LLC is not just another IT service provider. We are your strategic partner in navigating the complexities of today’s digital world. Our holistic approach to IT management, cloud adoption, cybersecurity, and networking is designed to empower your organization, whether it’s a government entity, a private company, or a small business.
Based in Haymarket and serving the broader Northern Virginia area, Cloud2E LLC is committed to delivering cybersecurity solutions that are not only effective but also forward-thinking. Trust us to be the comerstone of your digital transformation journey, ensuring your IT infrastructure is robust. Feel free to reach out to us for a no obligation discussion of your needs.









